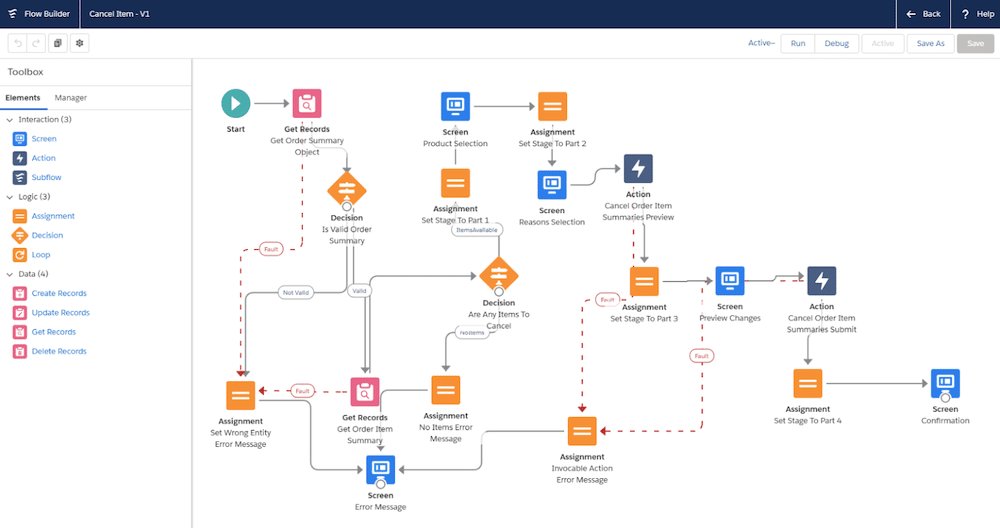
The software that
learns your business
through an AI interface,
but executes with
mathematical certainty.
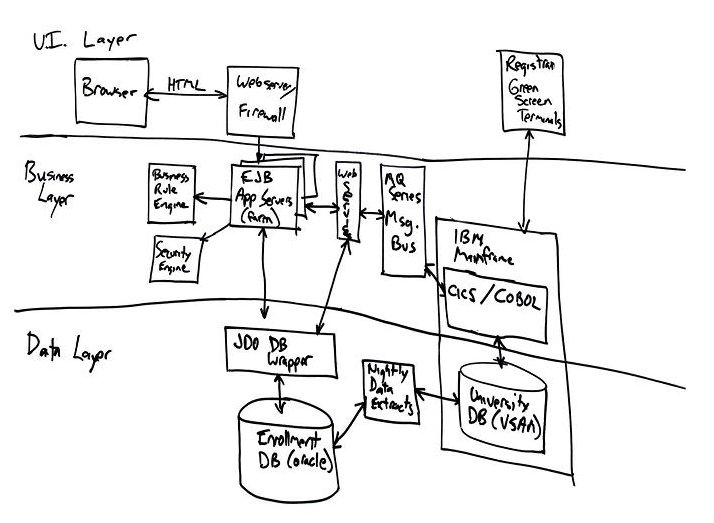
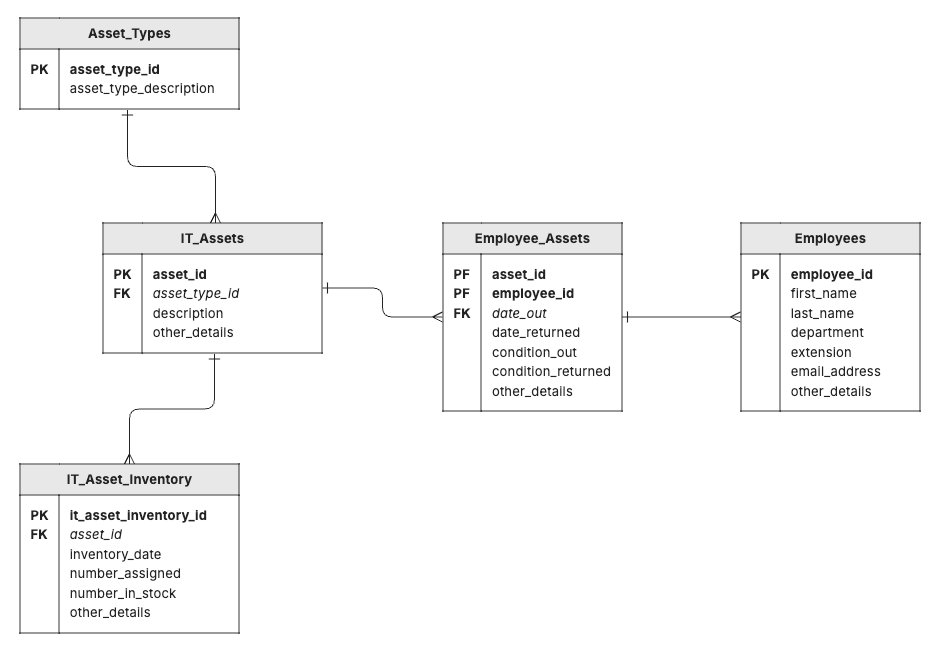
Flowsiti connects mid-stream to your existing reality. It does not require a clean slate. It ingests legacy systems, live configurations, documents, metadata, and tribal knowledge, any source, any format, any point in the lifecycle.